Software is no longer merely an analytical tool; it is the definitive reality of capital.
Westwyrd Ventures architects the absolute operating system for institutional financial defense. We transform legacy Real-World Assets from idle, vulnerable legal contracts into weaponized, cryptographically-sealed smart instruments.
Zero-Latency Cryptographic Mapping.
Bypassing the era of falsifiable paper-trail certificates, Absolute Custody is proven dynamically via structural on-chain telemetry mapping. We permanently sever exposure to the fractional retail margin.
Eliminating the Custodial Illusion.
Traditional custody without cryptographic attestation is a regulatory mirage. We replace human institutional latency, legal ambiguity, and manual compliance layers with definitive, autonomous mathematics.
Deep Tesseract Situational Awareness.
Deploying 4D hypercube visualization pipelines to monitor adversarial variants. Every interaction and cross-chain taint vector is geometrically modeled to predict systemic threats before they manifest on the ledger.
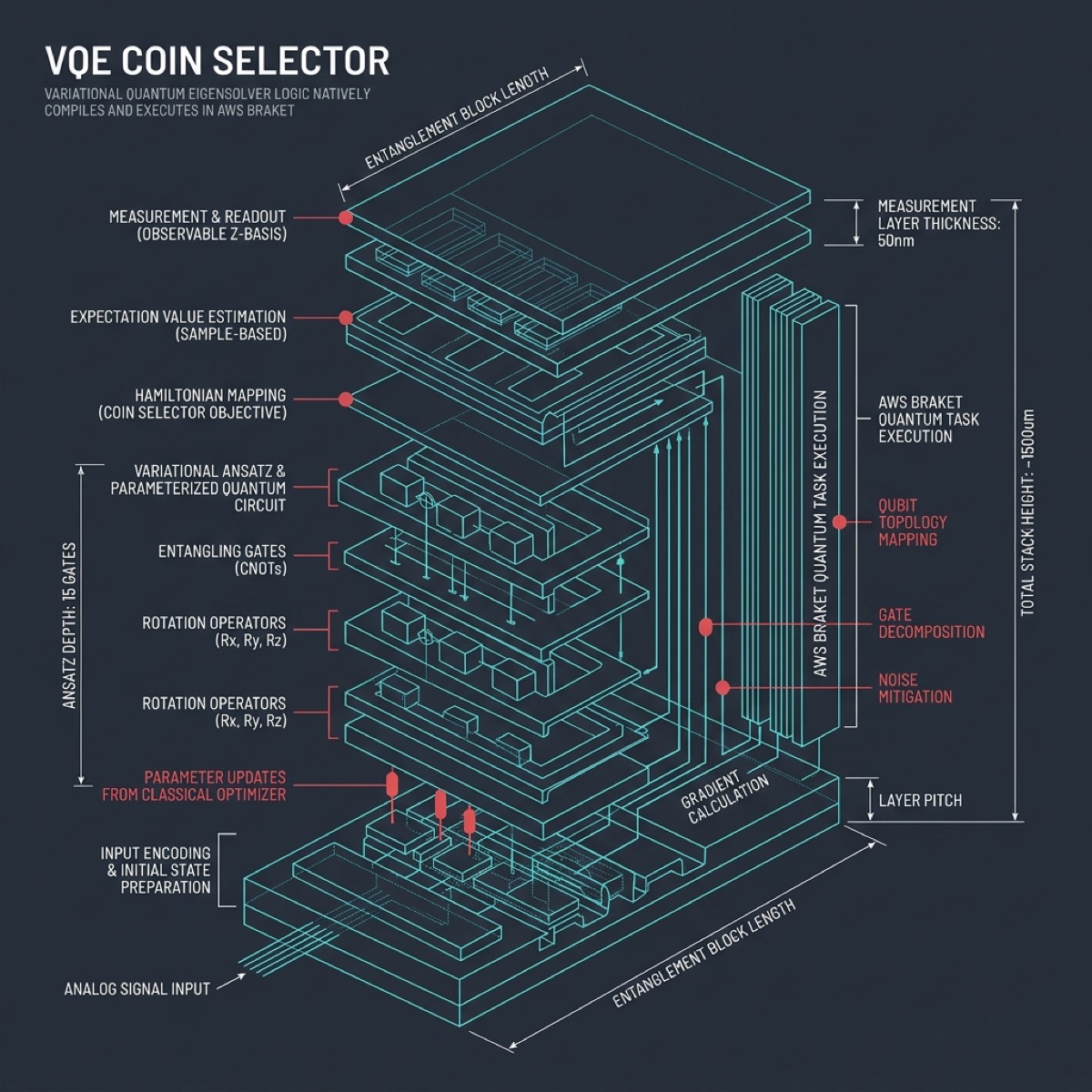
Native Quantum QPU Attestation.
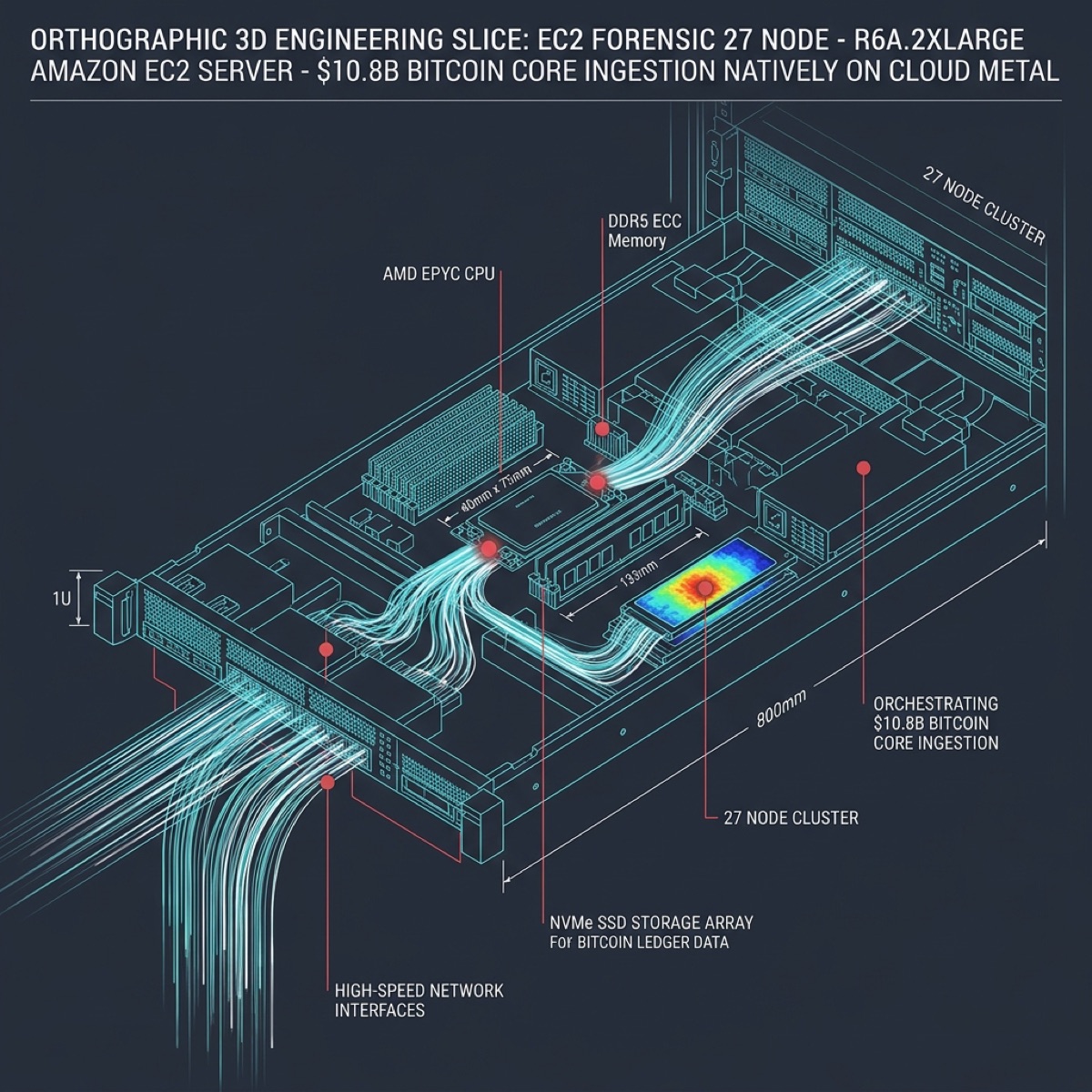
Uncompromising hardware-level execution. Featuring physical QPU attestation via Rigetti Aspen-M-3 and IBM Heron r2 clusters, integrated deeply with Apple M-Series Silicon for local cognitive orchestration.
Enterprise At The Edge.
Designed for operations in Zero-Telemetry environments. The matrix automatically forces an encrypted 'Drip-Relay' sequence, rendering hostile physical extraction utterly powerless through localized node autonomy.
Continuous ARC Testing.
Dynamically validating the cognitive integrity of our synthetic substrates through rigorous Abstraction and Reasoning Corpus (ARC) dimensions. AI agents are continually graded on spatial orientation and impedance tracking.
Cognitive Visualization: Attention Lab.
Located within the ABRAXAS-1 Meta-Deterministic Evidentiary System. We dynamically map attention mechanisms and cognitive load across Apple Silicon Metal GPU rendering pipelines, projecting event-sourced forensic archival.
Meta-Deterministic Evidentiary Engine.
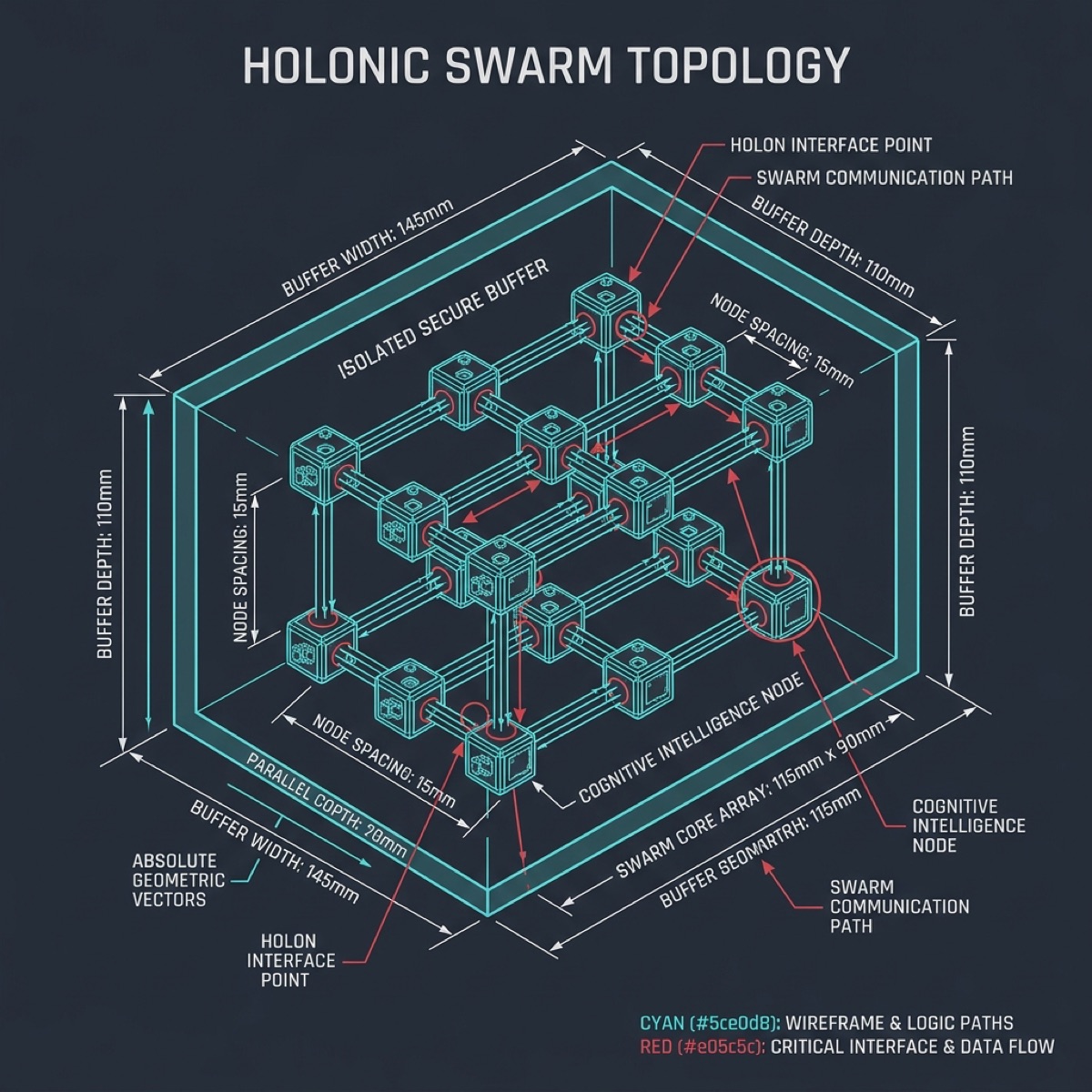
ABRAXAS-1 deploys holonic agent swarms within a Zero-Separation analysis environment. Root-cause telemetry grids isolate and anchor forensic truth using Poseidon hash verification.
Absolute Causality Tracing.
Integrating Poseidon Shard Services with native Swift/Metal engines to generate irrefutable cryptographic evidence. Every state transition is anchored, enabling absolute causality mapping.
Audio-Reactive Voxel Geometry.
High-performance SDF raymarching and spatial audio engines render immense voxel grids locally. We bypass cloud-compute latencies by executing spatial indexing directly on native hardware.
The Protocol of Kinetic Silence.
The 161,653 BTC Treasury is held in absolute Deep Cold Storage. The assets never move, are never traded, and are strictly non-rehypothecated. We activate external liquidity natively via Sovereign Lombard credit lines, preserving the mathematical "Gold Standard" without compromising collateral integrity.
Explosive Swarm Cohesion.
State operations dynamically simulate high-density schooling structures—mirroring deep-market directional flows. Bioluminescent transient cascades respond explosively in the kinetic vector field.
Gravitational Planetary Orbitals.
Particles collapse into discrete spherical bodies, tracing immense orbital paths around a central star matrix. Gravity responds directly to the low-frequency transients.
The Custodial Illusion
Defending Against Ontological Drift.
Wall Street and legacy banking infrastructures are collapsing under the weight of their own latency. They operate on a disparate, fragile constellation of centralized databases, human committees, and paper-based legal fictions that invariably fail during moments of critical market stress.
Any capital allocator anchoring their wealth to the unverified public web is securing their survival to a mathematically poisoned mirage. Westwyrd permanently severs all exposure to the unsophisticated fractional retail margin, establishing native, zero-latency execution.
Traditional custody without cryptographic attestation is an illusion. Our solution is the Absolute Remedy—replacing human institutional latency, legal ambiguity, and manual compliance layers with definitive, autonomous mathematics.
Architectural Pillars
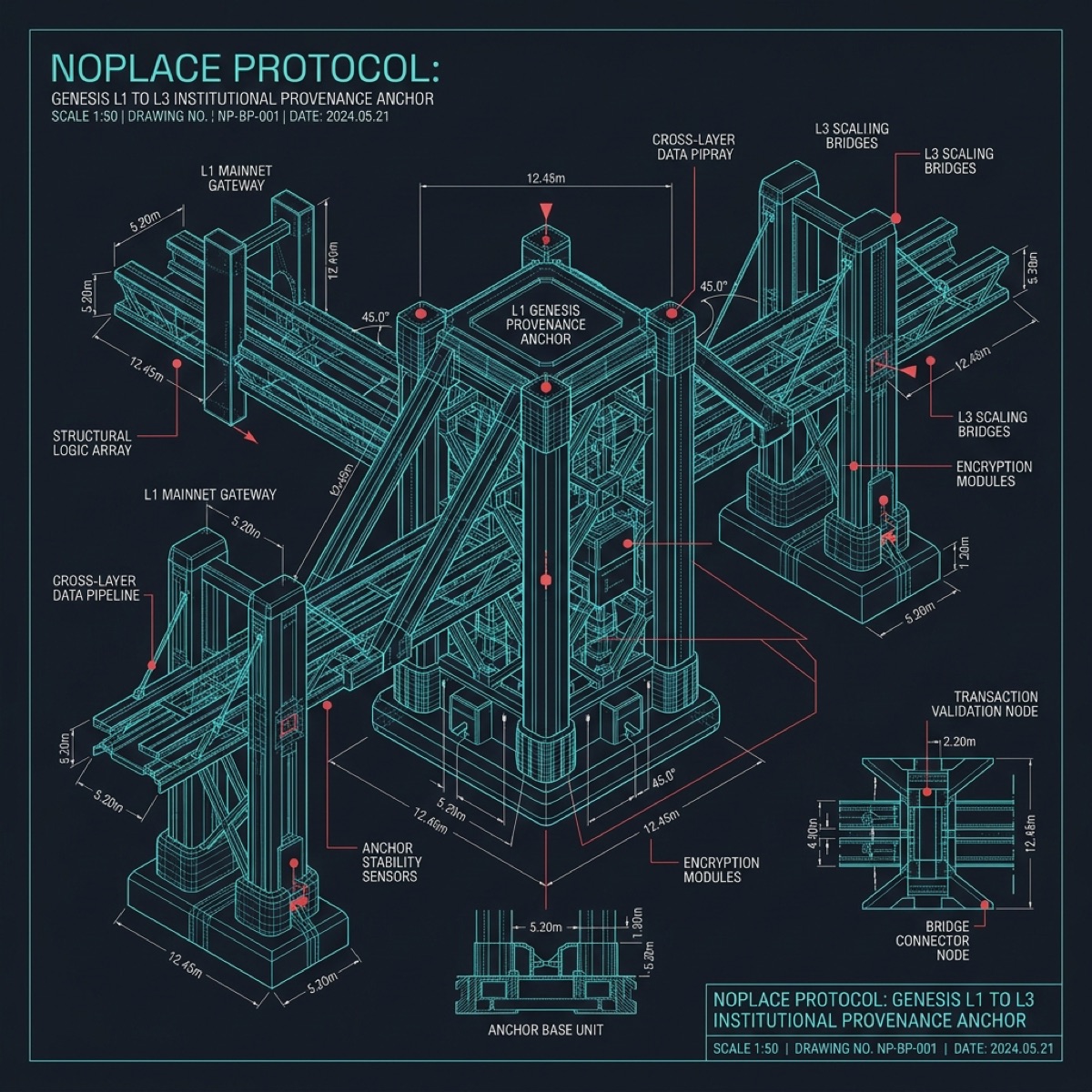
End-to-end institutional infrastructure from hardware attestation through cryptographic settlement finality.
Utilizing the SAP-F Containment Sieve, we bypass human committee routing entirely. If protocol failure or adversarial exploits are detected, encrypted kill-signals execute an absolute lockdown of physical fiat treasury operations in under 100 milliseconds.
Pursuant to Uniform Commercial Code § 8-106(d)(2), Westwyrd bridges legacy legal ownership with on-chain absolute finality. The Securities Account Control Agreement integrates traditional broker-dealers directly into the smart contract execution environment.
Uncompromising hardware-level execution. Featuring QPU attestation via Rigetti Ankaa-3 and IBM Heron r2 clusters, integrated deeply with Apple M-Series Silicon for local VVALT cognitive orchestration and 4D Tesseract forensic telemetry.
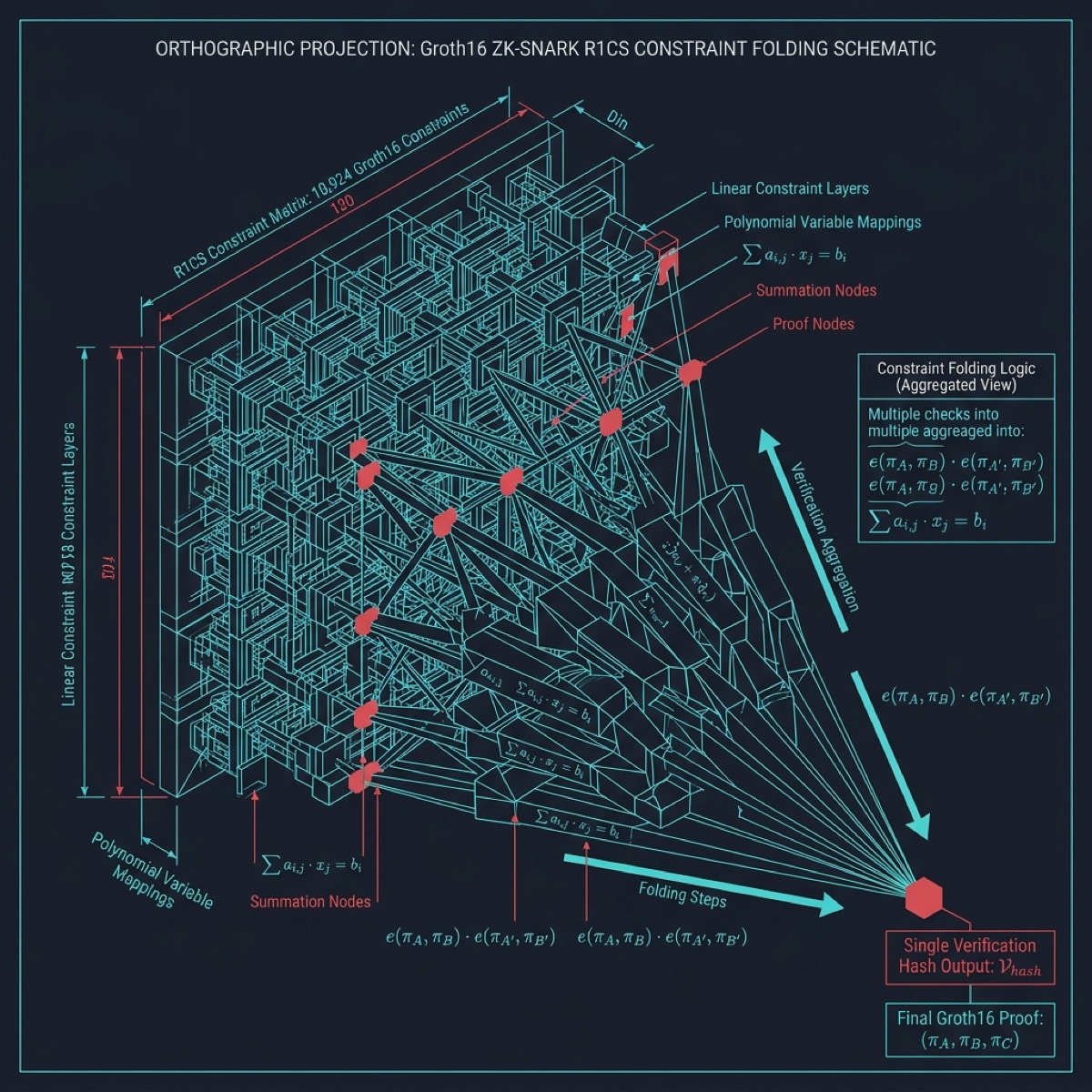
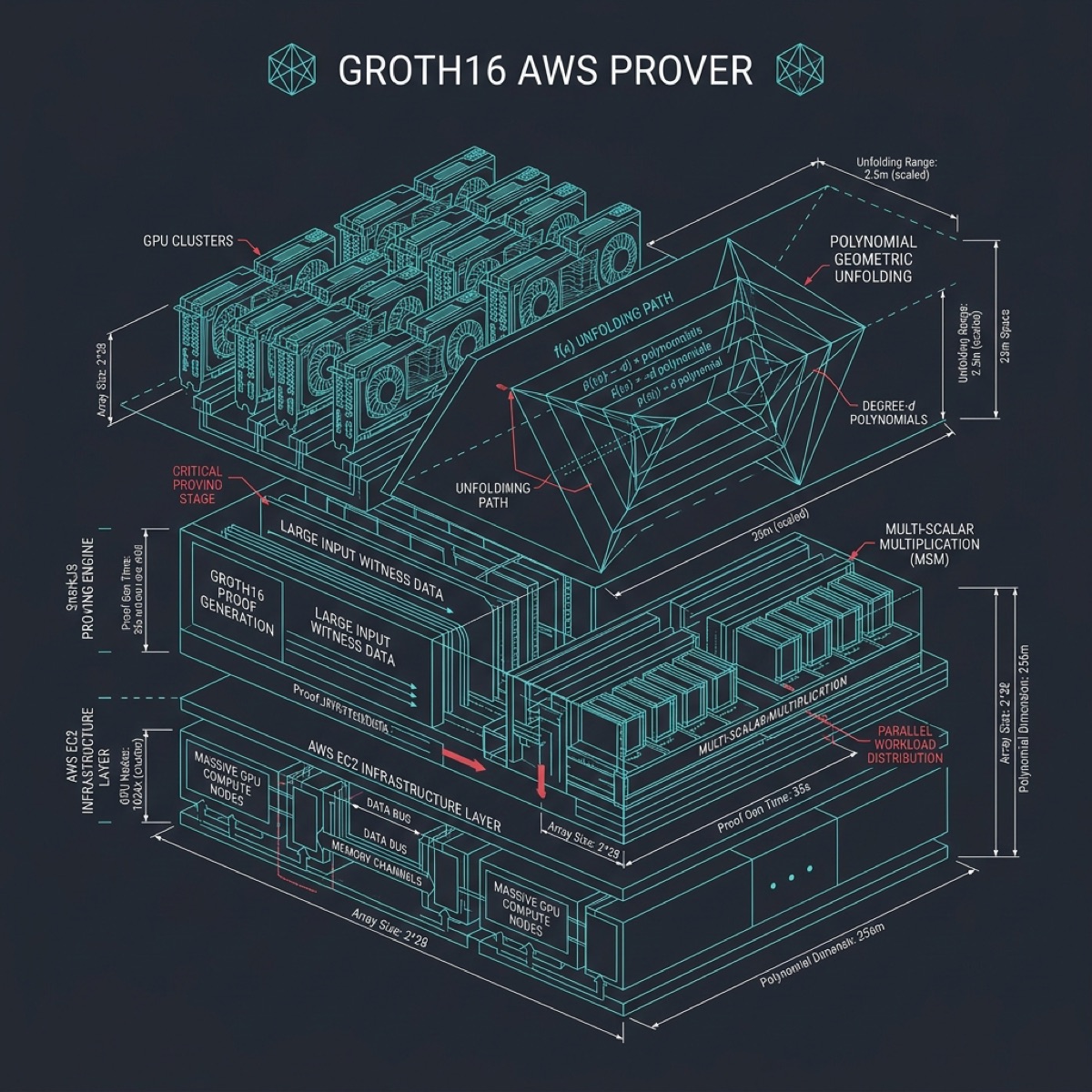
We mathematically solve the institutional compliance paradox. ZK-SNARK proofs verify to global regulators that KYC checks and reserve balances are pristine, while immediately destroying raw PII from volatile caches to eliminate database vectors.
Threat Mitigation & Containment
Algorithmic neutralization of adversarial liquidity vectors.
The Adversarial Legacy Allocation
During a high-velocity intake phase for a syndicated counterparty, Westwyrd's SAP-F architecture detected critical Virtual Data Room (VDR) variance and active forensic obfuscation. The adversarial principal operated under an illicit structural delusion, attempting to weaponize our zero-knowledge protocols as an exit-liquidity trap—seeking to instantly digitize strictly unverified, legacy assets into scalable High-Frequency Trading capital. The primary objective of the counterparty was to extract liquid utility while forcing all systemic AML/KYC regulatory liability exclusively onto the institutional node operators.
Protocol Execution
- Algorithmic Hold TriggeredPre-deployment telemetry isolated the variance. Cryptographic parameters controlling the genesis allocation were functionally severed, simulating a terminal bricking of the asset transfer vectors laterally.
- Asymmetric Liability ShieldingBy halting physical-to-digital mapping upon footprint variance, the protocol systematically insulated the ledger. We refused to manufacture institutional risk on behalf of external shadow-state maneuvering.
- Zero-Separation ArchivalSynchronous communications were permanently suspended to blockade linguistic manipulation. All forensic telemetry—including SQLite browser artifacts of the obfuscation attempt—was aggregated, sealed, and firmly stored.
Structural Forensic Verification
Kinetic Disconnect Protocols
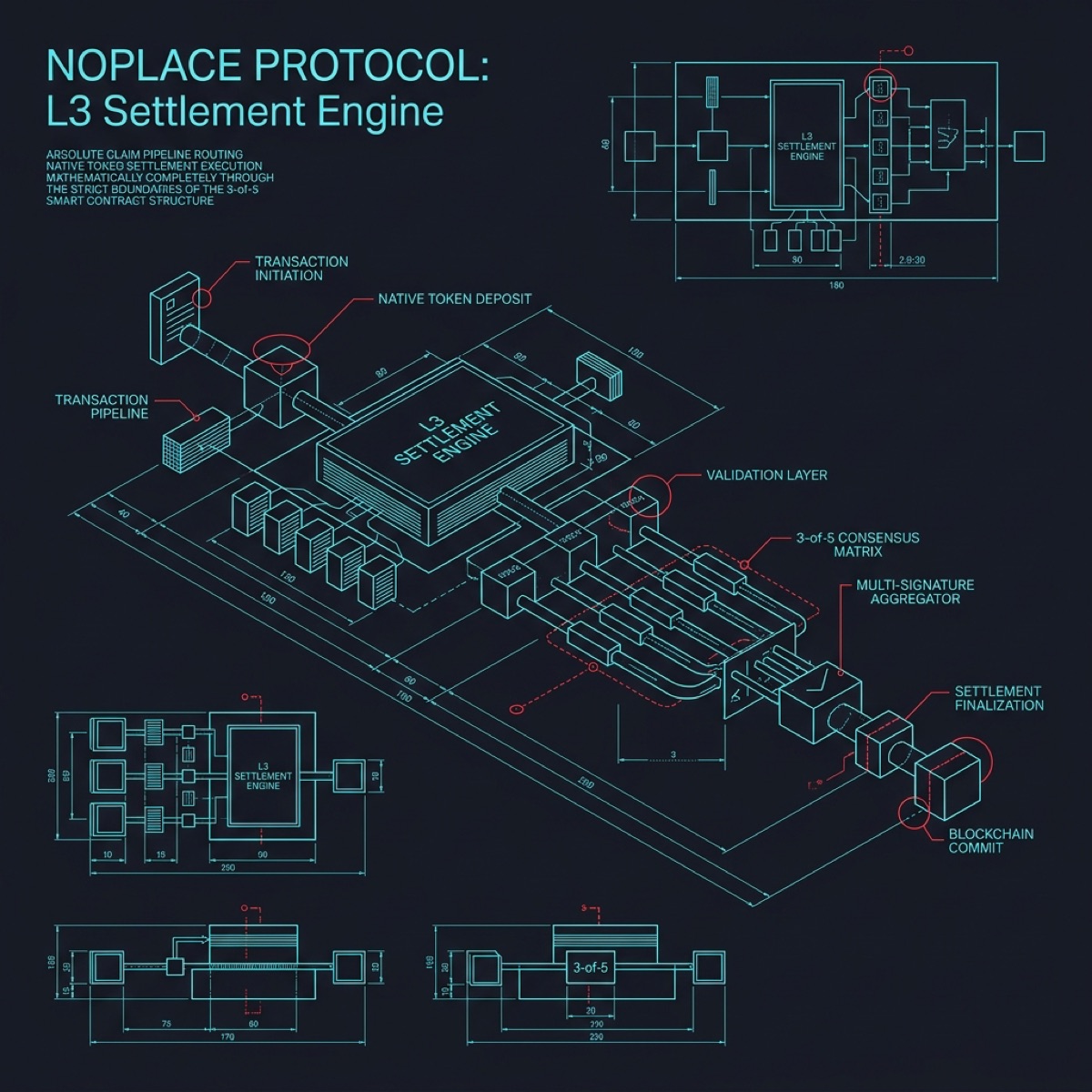
In the event of attempted physical coercion, domestic interference, or localized infrastructure sabotage (e.g. forced identity claims), our NOPLACE Protocol automatically deploys Scenario Gamma.
This forces the node matrix into an encrypted "Drip-Relay" sequence and defaults to Absolute Kinetic Silence. Access to the treasury is preserved through Math-Only Authority deployed from Zero-Telemetry operational zones, rendering hostile physical extraction utterly powerless.
17-Domain Verification Matrix
Westwyrd doesn't rely on probabilistic audits. Master legacy inputs traverse a rigorous 17-Domain forensic pipeline running across high-compute Apple M-Series matrices before striking the mainnet.
Raw data is analyzed across temporal latency, fee profiling, Benford statistical deviation, and cross-chain taint mapping. This yields an uncompromising 'Institutional Grade' score matching top-tier regulatory standards, compressed precisely into a single zero-knowledge Merkle Root for global dissemination.
Cryptographic Validation
Bypassing the era of falsifiable paper-trail certificates, Absolute Custody is proven dynamically via structural on-chain telemetry mapping.
By tracking low-velocity dormancy cycles, ensuring multi-path randomized HD derivation via Poseidon hashes, and executing rolling OFAC matching, Beneficial Ownership is inherently tied to the cryptographic witness string. No third-party trust agent is required to enforce the truth.
Institutional Architecture Atlas
Palantir-grade topological cross-sections of the Paramount Quantum FaaS infrastructure.