Security Architecture
Westwyrd is designed under the assumption of adversarial conditions. Security is enforced across cryptographic, infrastructure, and application layers.
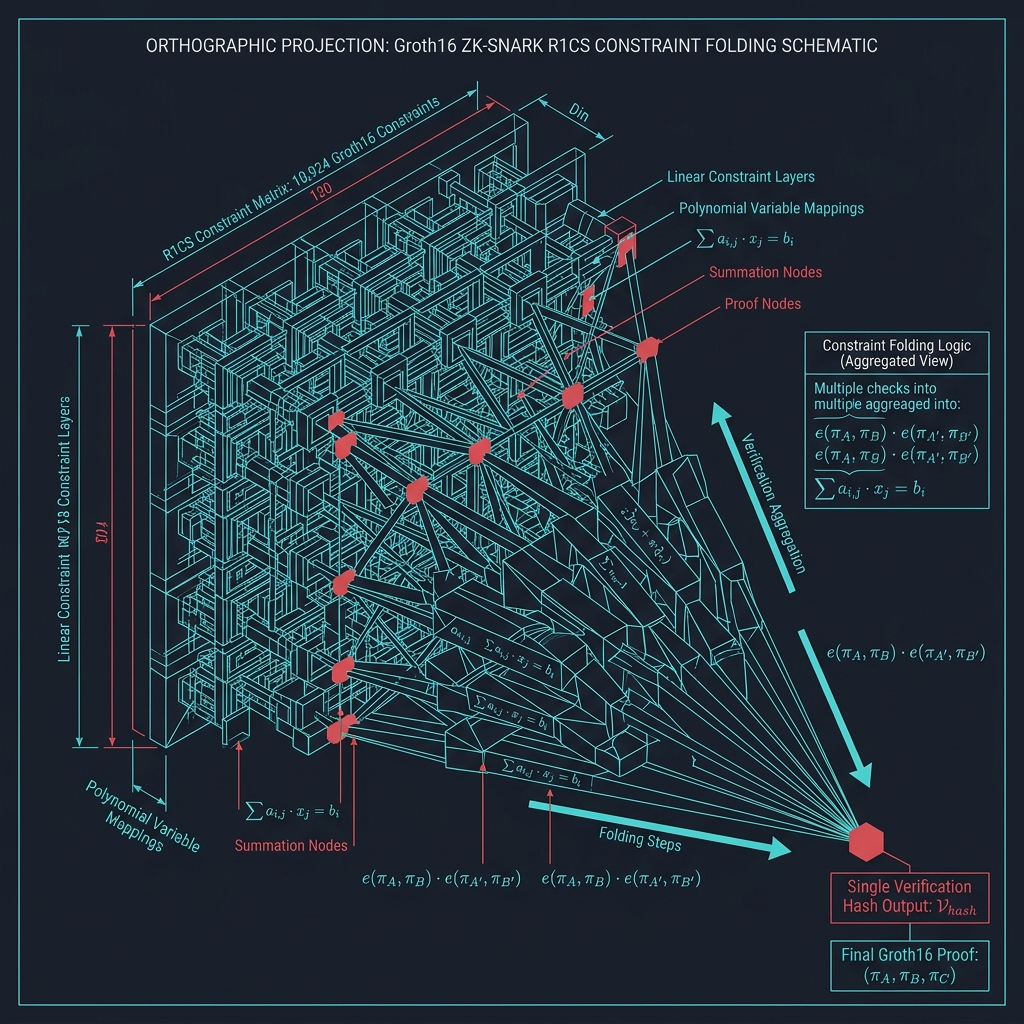
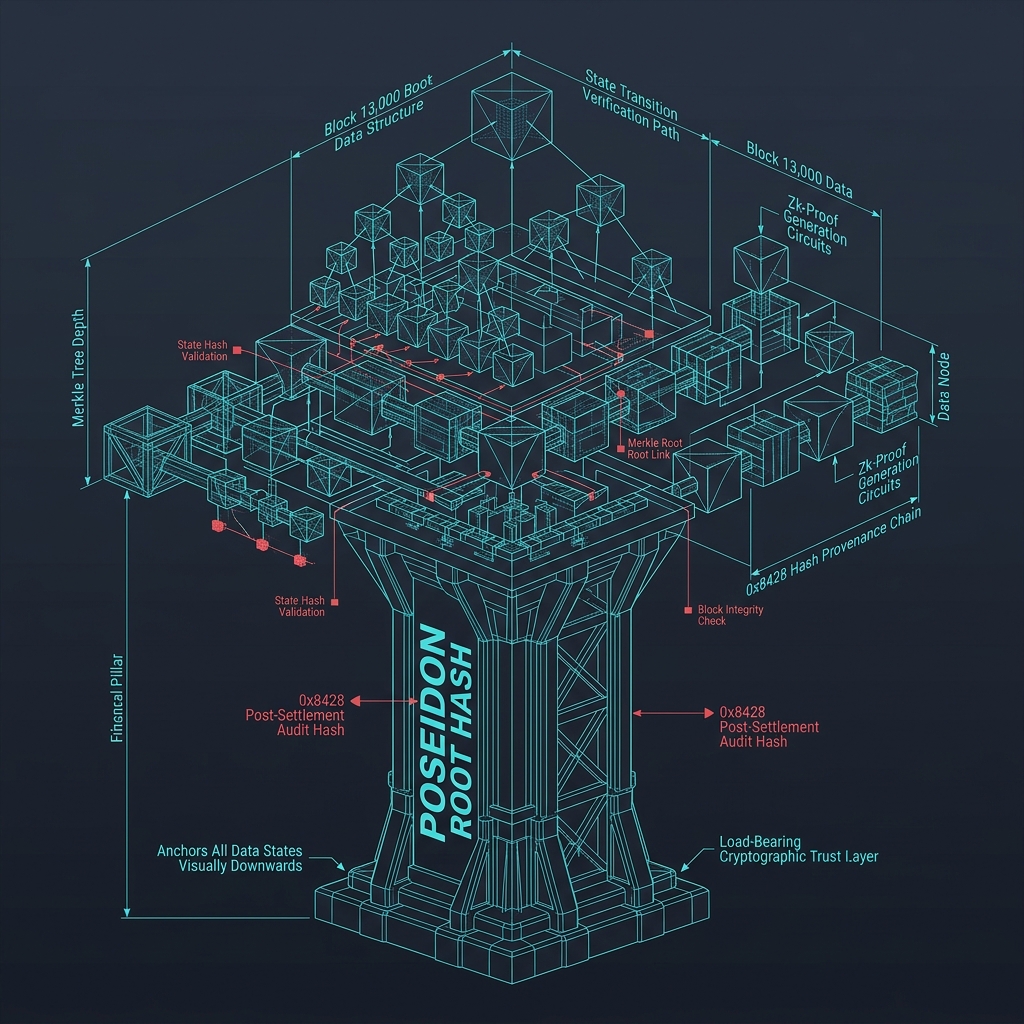
Cryptographic Layer
Groth16 · Poseidon · Circuit-to-Contract Binding
- ■Groth16 zero-knowledge proofs over BN254 — selected for constant-time verification and minimal on-chain footprint
- ■Poseidon hash commitments with fixed parameters — algebraically optimized for ZK circuit efficiency
- ■Circuit-to-contract binding to eliminate proof mismatch risk — deployed verifiers are deterministically derived from compiled circuits
All cryptographic operations are deterministic. No randomness-dependent primitives are used in production proof generation. Verification keys are derived from the circuit compilation output and are immutably bound to the on-chain verifier contracts.
Infrastructure Layer
Multisig · Role Separation · Domain Isolation
- ■Multisignature governance with enforced role separation — no single key can authorize critical operations
- ■Administrative control minimization through role renunciation — privileged roles are explicitly revoked after deployment
- ■Layered execution model isolating reserve, bridge, and execution domains — failure in one domain cannot propagate to others
Application Layer
Deterministic execution only
- ■Deterministic execution paths only — all outputs are derivable from inputs
- ■No hidden state mutation or non-verifiable logic
- ■Strict interface boundaries for all API surfaces — no ambient authority or implicit permissions
Monitoring & Response
Real-time detection and forensic traceability
- ■Real-time anomaly detection via arbitration systems
- ■Event-driven alerts across on-chain and off-chain environments
- ■Full forensic traceability through graph-based analysis systems
- ■Incident response procedures with defined escalation paths
The monitoring infrastructure operates independently of the execution layer. Detection systems cannot be disabled or circumvented through protocol interactions. All alerts and events are recorded in append-only audit logs.