Red Team Operations
Adversarial Testing & Red Teaming
Westwyrd operates under continuous adversarial testing conditions. The system is treated as a hostile environment, and all components are regularly subjected to simulated attack scenarios.
Testing Methodologies
- ■White-box testing with full protocol access — internal teams with complete source code and architecture knowledge
- ■Black-box external attacker simulations — independent testers with no prior knowledge of system internals
- ■Grey-box partial disclosure scenarios — controlled information asymmetry testing
Technical Figure
RED-FRG-008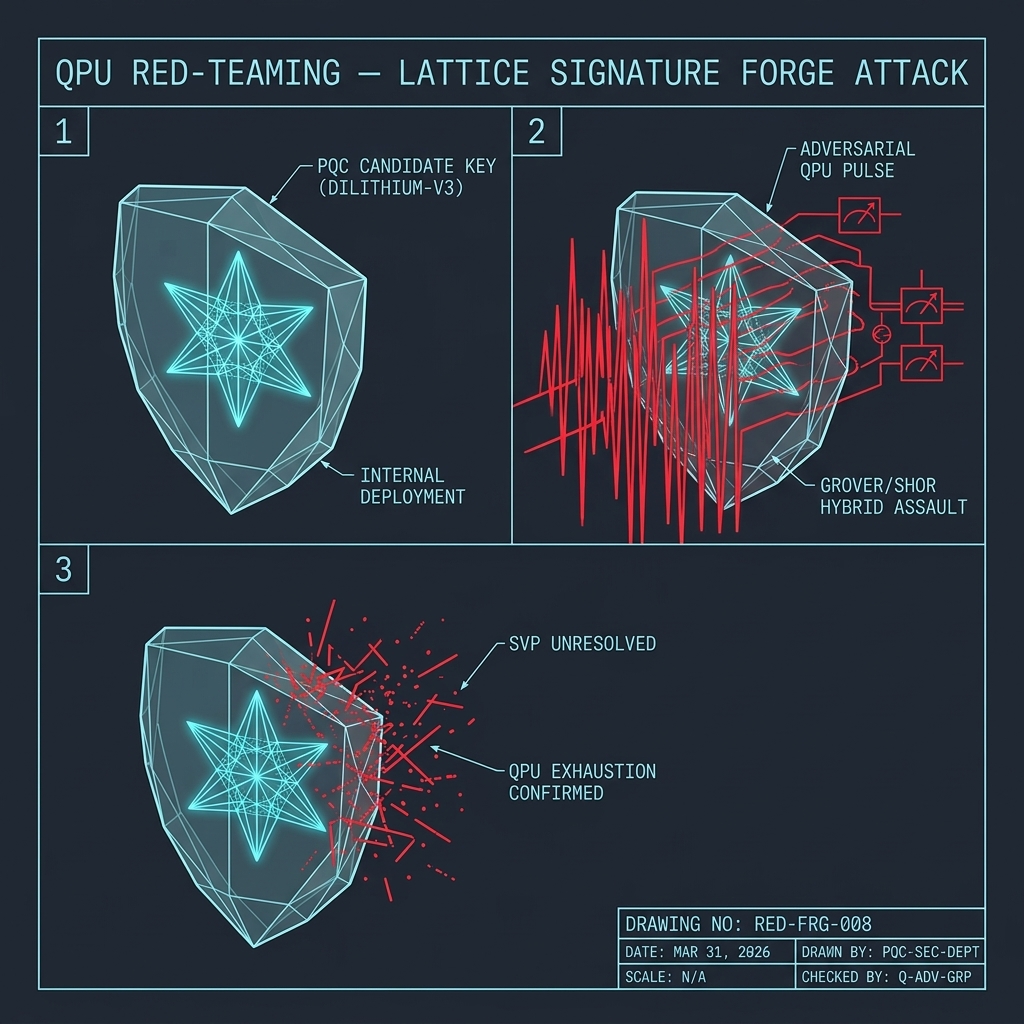
Testing Scope
Comprehensive coverage across all attack surfaces
- ■Smart contracts and verification logic
- ■Bridge and settlement pathways
- ■API and interface surfaces
- ■Governance and control mechanisms
- ■Zero-knowledge circuits and proof validation
Testing Phases
PHASE 01
Reconnaissance
Surface enumeration
PHASE 02
Mapping
Attack surface analysis
PHASE 03
Identification
Vulnerability discovery
PHASE 04
Exploitation
Controlled breach testing
PHASE 05
Remediation
Fix verification
Advanced Testing
Beyond standard penetration testing
- ■Proof forgery simulations — adversarial attempts to generate valid proofs for invalid state transitions
- ■Economic attack modeling — oracle manipulation, liquidity stress, MEV extraction scenarios
- ■Governance injection attempts — unauthorized proposal execution and voting manipulation
- ■Circuit integrity validation under adversarial conditions — constraint satisfaction attacks
Technical Figure
ADV-DEC-005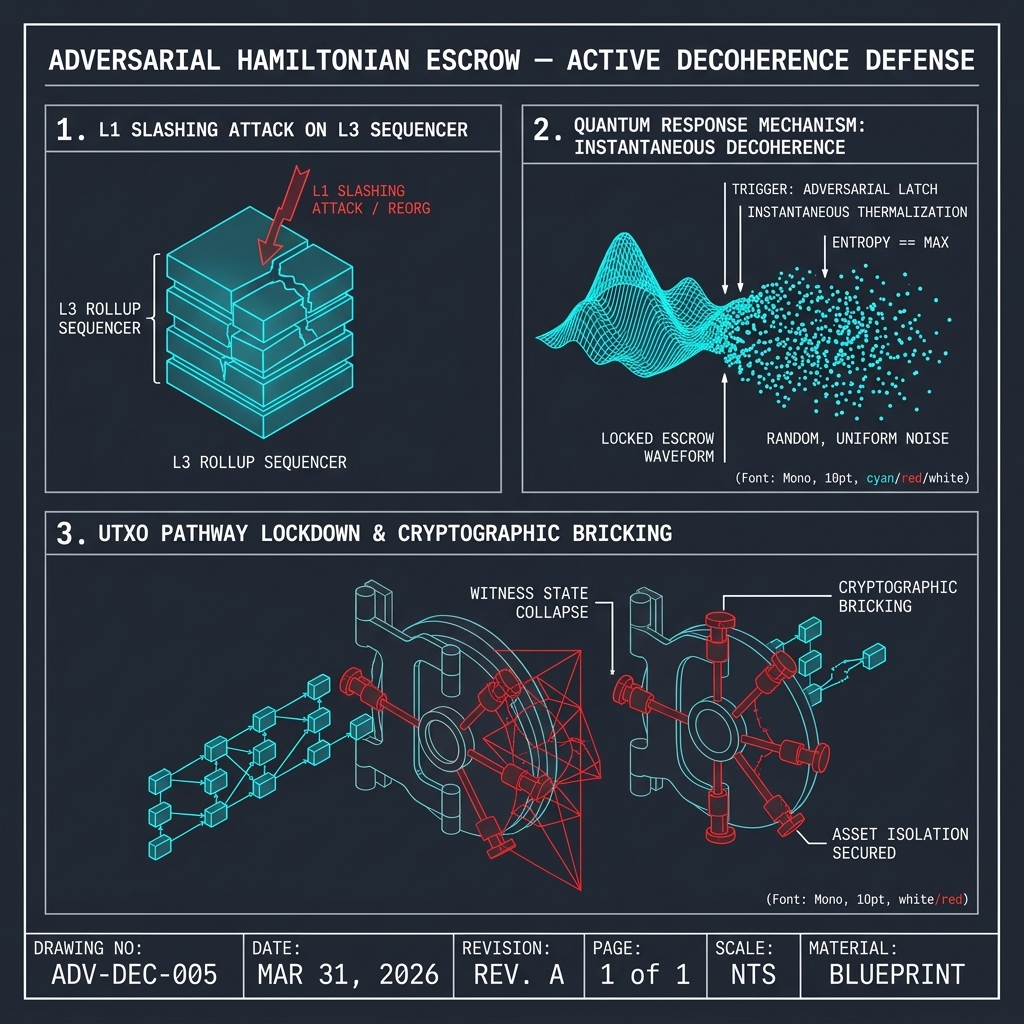
Testing is continuous and event-driven, not periodic. New attack vectors are incorporated into the testing framework as they are discovered in the broader ecosystem. All findings are documented, remediated, and verified before deployment.