Westwyrd Protocol
Westwyrd is a deterministic execution and verification layer designed for institutional-grade settlement. The system enforces cryptographic validation of state transitions through zero-knowledge proofs, eliminating reliance on trust-based intermediaries.
The protocol does not custody assets, make discretionary decisions, or introduce probabilistic execution paths. All outcomes are derived from verifiable inputs, circuit-bound constraints, and on-chain enforcement.
Westwyrd operates across a layered architecture designed to ensure that every unit of value, state transition, and settlement outcome is mathematically provable, independently verifiable, and resistant to manipulation.
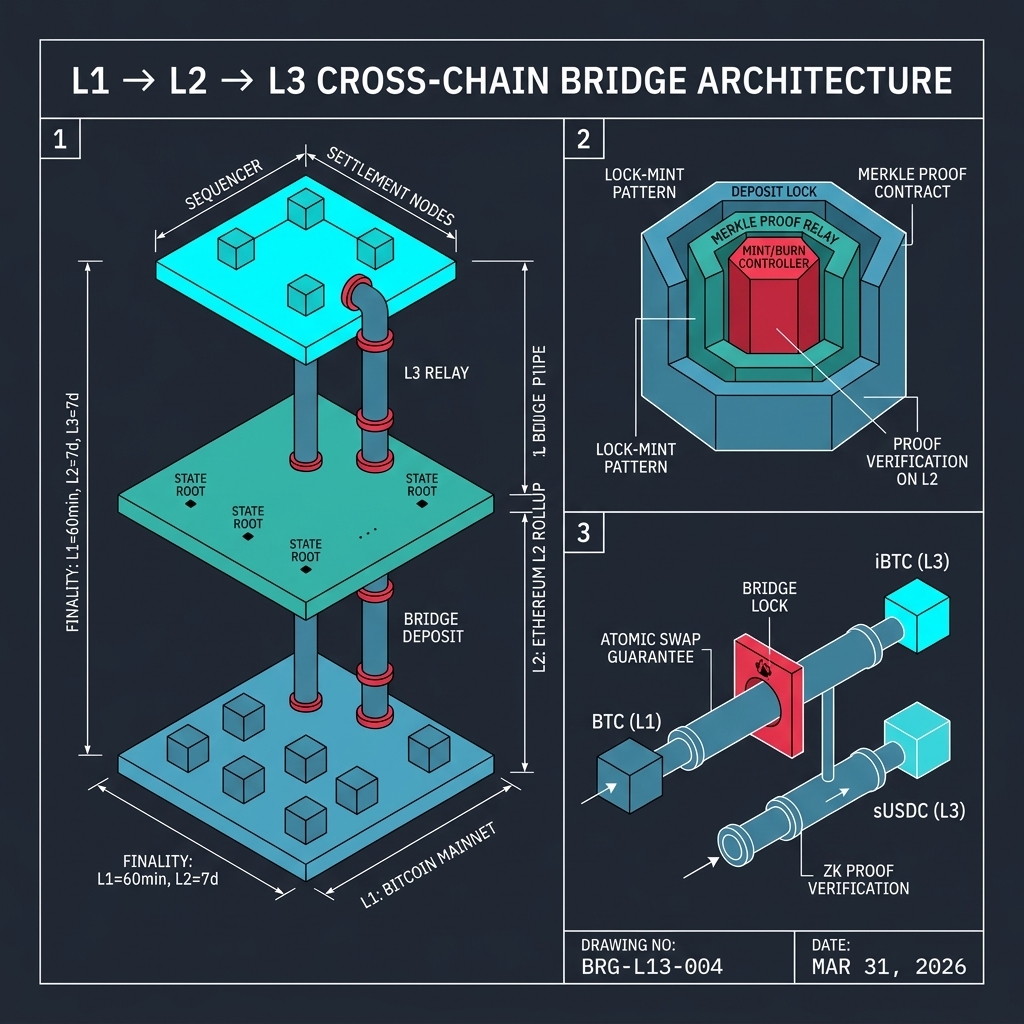
Layer 1 — Settlement Foundation
Reserve anchoring and base settlement guarantees
Layer 1 establishes the immutable reserve anchor. All base assets are verified at this level through cryptographic proofs of inclusion. Settlement guarantees are enforced through smart contract logic that is formally verified and bound to specific circuit constraints.
The L1 layer serves as the root of trust for the entire protocol stack. No higher-layer operation can override or circumvent the settlement guarantees established here.
Layer 2 — State Transport
Bridging and state propagation
Layer 2 manages the propagation of verified state between settlement domains. Bridge operations are secured through Merkle proofs of inclusion, watchtower monitoring, and challenge-response mechanisms.
State transitions at this layer are validated through zero-knowledge proofs before propagation. No unverified state is permitted to cross domain boundaries.
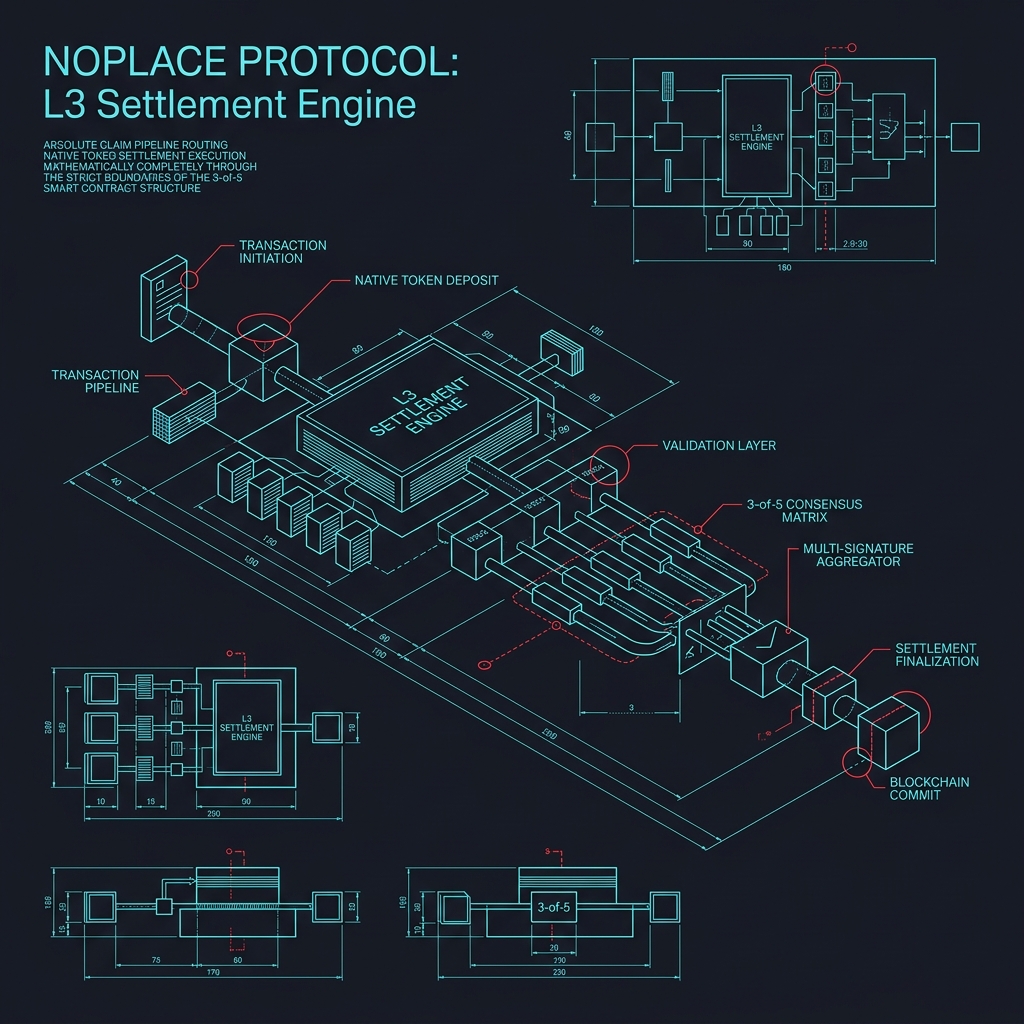
Layer 3 — Execution Fabric
Execution integrity and verification
Layer 3 enforces execution integrity through deterministic computation. All operations are bound to circuit constraints, and every state transition produces a verifiable proof of correct execution.
The execution fabric operates as a sovereign rollup with its own sequencer, block production, and fraud proof system. Settlement finality is achieved through proof verification on the base layer.
Design Principles
- ■Every unit of value is mathematically provable and independently verifiable
- ■State transitions are deterministic and circuit-bound
- ■No probabilistic execution paths or discretionary decision points
- ■Settlement outcomes are resistant to manipulation through cryptographic enforcement
- ■The protocol does not custody, rehypothecate, or control user assets