Trust Center
Westwyrd maintains a continuous public assurance surface designed to provide immediate verification of security posture, operational integrity, and system behavior.
Security Model
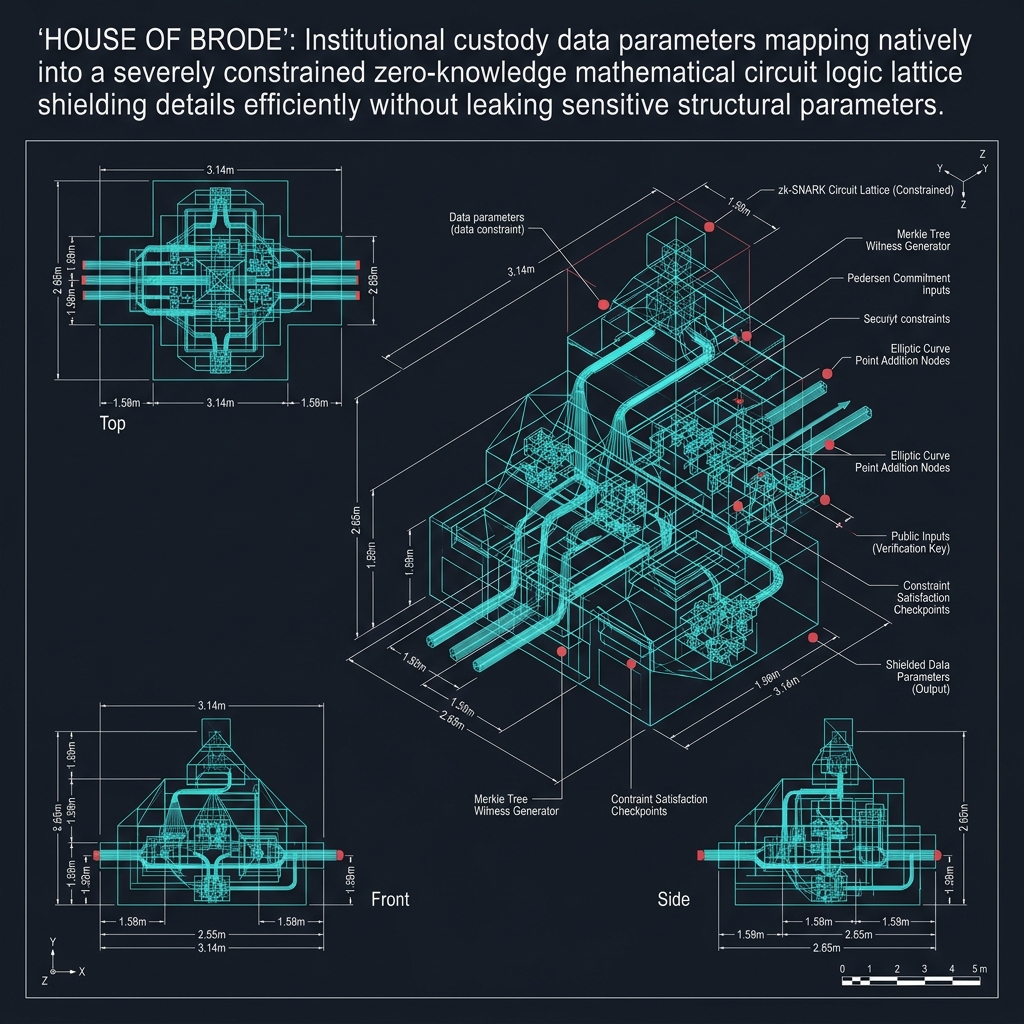
Verification-first architecture
The protocol enforces a verification-first architecture. Zero-knowledge proofs are required for state transitions, and smart contracts are bound to specific circuit constraints to prevent divergence between proof systems and execution logic.
All cryptographic primitives are selected for their formal security guarantees and resistance to known attack vectors. No custom or unaudited cryptographic constructions are used in production.
Custody Model
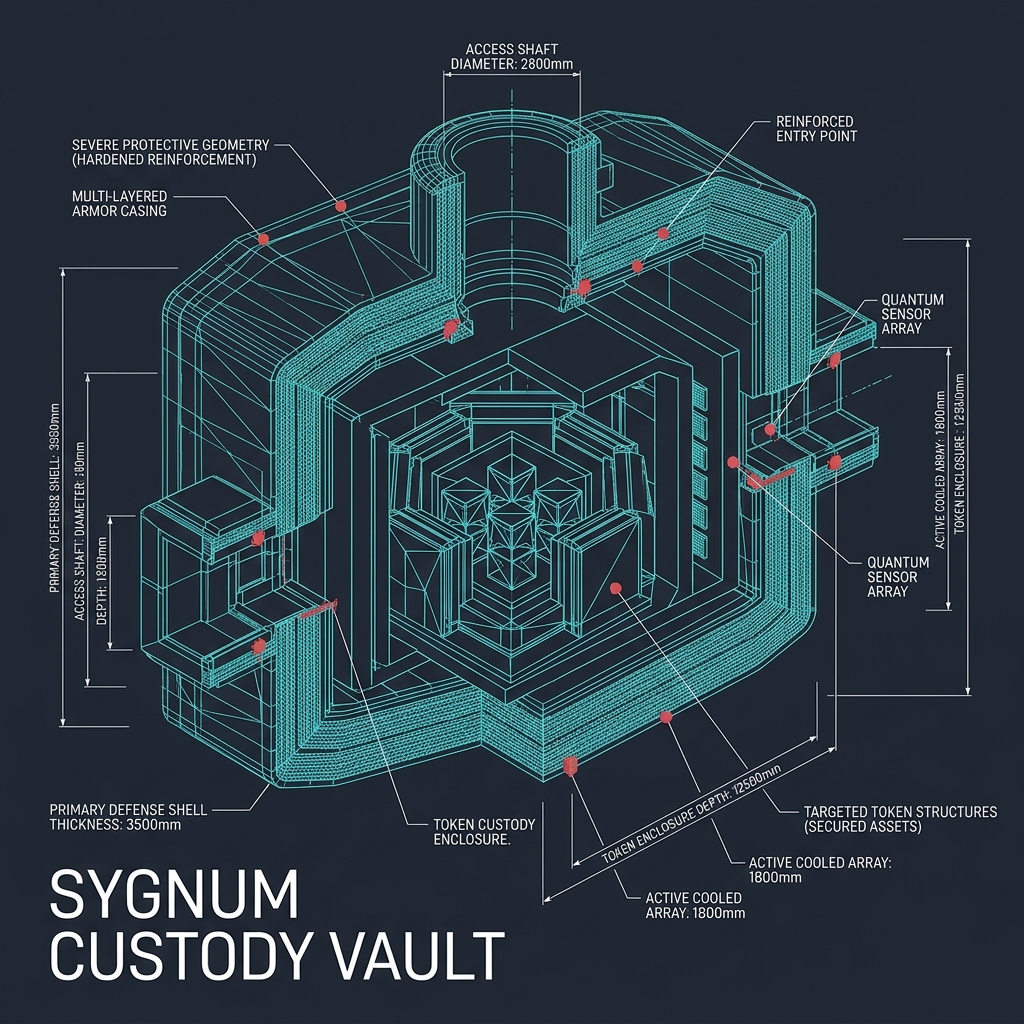
Non-custodial by design
Westwyrd does not take custody of user assets. The protocol verifies claims about assets but does not hold, rehypothecate, or control them.
Asset ownership remains with the user at all times. The protocol provides verification infrastructure that allows users to prove ownership and authorize state transitions without surrendering control.
Data Handling
Minimal collection, deterministic processing
The system minimizes data collection. No behavioral telemetry is required for protocol operation. Inputs are deterministic and user-provided.
All data processing follows the principle of minimal disclosure. Zero-knowledge proofs allow verification of claims without revealing underlying data.
Operational Transparency
- ■System uptime and availability are continuously monitored
- ■No unresolved critical incidents have been recorded
- ■All security events are logged and traceable
- ■Verification artifacts are maintained and available for inspection
Audit Posture
Westwyrd maintains internal verification artifacts and formal proofs that bind cryptographic circuits to deployed contracts. Public-facing audit summaries are made available where appropriate without exposing sensitive attack surfaces.
Formal verification using Rocq/Coq proof assistants ensures that protocol invariants hold under all execution conditions. These proofs are maintained alongside the production codebase.